Types of hackers are not something we usually think about in our daily life.
Let’s not start this like a typical blog.
Instead, think about your daily routine.
You wake up, check your phone, open Instagram, reply to messages, maybe scroll through emails, and later make an online payment. Everything feels smooth, fast, and secure.
But here’s something most people never think about.
While you are using the internet so casually, there are different types of hackers in cyber security looking at the same systems in very different ways.
Some are trying to protect it.
Some are trying to break it.
And some operate somewhere in between.
Types of hackers in cyber security is something every beginner must understand.
Understanding Types of Hackers in Cyber Security
Before we go deeper, let’s clear one of the biggest misconceptions.
Hacking is not always illegal.
In simple terms, hacking means identifying weaknesses in a system.
What truly matters is what happens after finding that weakness.
- If someone finds a problem and fixes it → it is helpful
- If someone finds a problem and misuses it → it is harmful
The real difference is not skill. It is intention.
Two people can have the same knowledge, tools, and access, but their mindset decides whether they become a protector or an attacker.
1. White Hat Hacker in Cyber Security
The first person is hired by the company.
He is given permission and a clear objective: find vulnerabilities before attackers do.
He carefully studies the system, tests different situations, and tries to break it in a controlled and legal way.
If he finds any weakness, he reports it immediately.
He does not steal data.
He does not misuse access.
He does not cause damage.
He improves security.
This is known as a White Hat Hacker, also called an ethical hacker.
How White Hat Hackers Work?
White hat hackers think like attackers but act responsibly.
Their work includes:
- Testing login systems
- Checking password strength
- Trying controlled access to restricted areas
- Analyzing how data is stored and transferred
Everything they do is authorized and legal.
Real-World Importance
Before launching new features, companies such as banks and e-commerce platforms hire ethical hackers.
Because fixing vulnerabilities early is much easier and cheaper than dealing with cyber attacks later.
2. Black Hat Hacker in Cyber Security
The second person is not hired.
He has no permission but still tries to break into the system.
His goal is to access data and misuse it.
This is a Black Hat Hacker.
How Black Hat Hackers Attack?
They use different techniques such as:
- Phishing links and fake websites
- Fraud emails and messages
- Malware and viruses
- Password cracking
- Exploiting software vulnerabilities
They often target regular users who are unaware of these risks.
Real-Life Situation
You receive a message that looks like it is from your bank.
It says your account will be blocked if you do not verify it.
You click the link and enter your details.
Within minutes, your account is compromised.
This is not a system error. It is a black hat hacker using simple tricks.
Impact of Black Hat Hackers
Their actions can lead to:
- Financial loss
- Data theft
- Identity misuse
- Business damage
- Loss of trust
3. Grey Hat Hacker in Cyber Security
Grey hat hackers fall somewhere between white and black hat hackers.
They may find vulnerabilities without permission but do not always misuse them.
Why They Are Different?
- They do not always follow rules
- They may not have harmful intentions
- They sometimes expect recognition
The Risk Factor
Even with good intentions:
- They access systems without permission
- They break legal boundaries
- They operate in a grey area
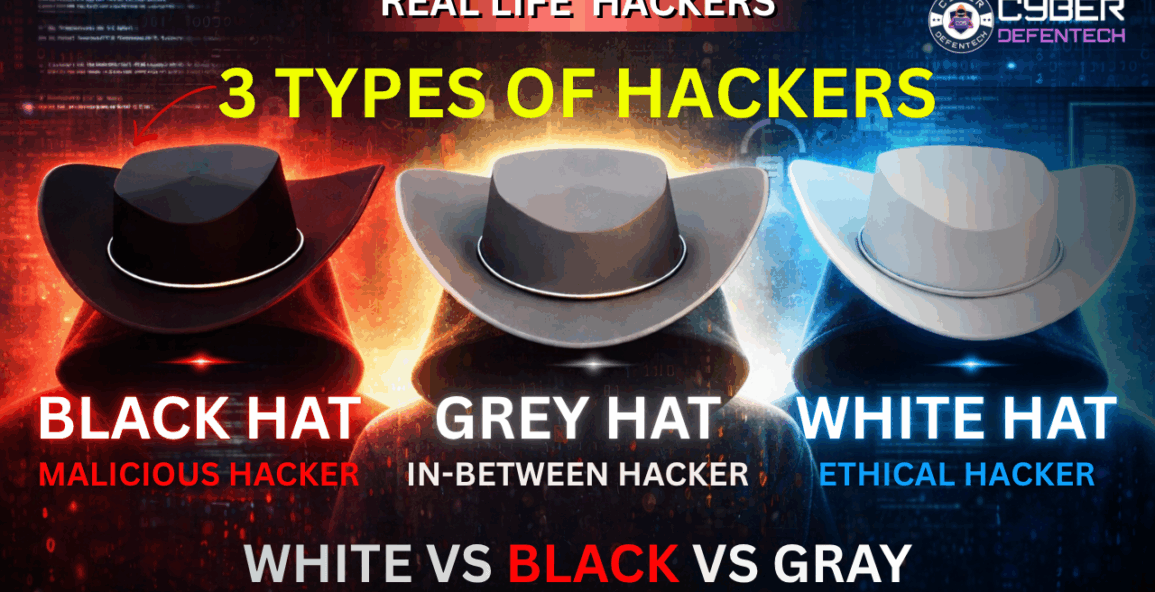
A Simple Way to Remember
- White Hat → Protects systems
- Black Hat → Attacks systems
- Grey Hat → Breaks rules but may not harm
Why Types of Hackers in Cyber Security Matter?
Understanding types of hackers in cyber security helps you:
- Stay safe online
- Protect your data
- Build a cyber security career
There are three main types of hackers in cyber security every beginner should know.
How You Can Start Your Cyber Security Journey ?
You do not need to learn everything at once.
Start step by step:
- Learn basic computer concepts
- Understand networking fundamentals
- Study common cyber attacks
- Practice in a safe environment
- Stay consistent and focused
Learning about types of hackers in cyber security is the first step.
Final Thought
The world does not need more attackers. It needs protectors.
The knowledge is the same.Your intention decides your path.
Start Your Cyber Security Journey Today
If you are serious about building a career in cyber security, this is the right time to begin.
At Cyber Defentech, we help beginners turn into skilled professionals with practical, real-world training.
- Beginner-friendly programs
- Step-by-step guidance
- Hands-on practical learning
- Career-focused roadmap
- Industry-level skills
Do not just use technology. Learn how to secure it.
📞 Call/WhatsApp: +91 8448046612
📧 Email: training@cyberdefentech.com
🌐 Website: cyberdefentech.com
Limited seats available. Take your first step today.


