Book a Trial Demo Class
Training Available 24*7 Call at 8448046612
Vulnerability Analysis stands out as a fundamental process in identifying and addressing potential weaknesses in systems before attackers can exploit them.
In the rapidly evolving digital landscape, cybersecurity has become a critical concern for individuals, organizations, and governments. As cyber threats grow in complexity and frequency, ethical hacking has emerged as a crucial line of defense.
This BLOG explores into the concept of vulnerability analysis in Cyber Security , examining its importance, methodologies, tools, challenges, and best practices.
What is Vulnerability Analysis ?
Vulnerability Analysis is the process of identifying, quantifying, and prioritizing vulnerabilities in a system. These vulnerabilities can exist in various forms software bugs, misconfigurations, weak passwords, unpatched systems, or outdated protocols. The goal of vulnerability analysis is to detect these weaknesses early so that they can be reduced before being exploited.
In the context of ethical hacking, vulnerability analysis is a proactive approach conducted by security professionals commonly known as “white-hat hackers” to assess and improve an organization’s security posture. Unlike malicious hackers, ethical hackers are authorized to perform these assessments and operate within legal boundaries.
Why Vulnerability Analysis is Important?
The importance of vulnerability analysis in ethical hacking cannot be overstated. Here’s why:
- Proactive Risk Management
By identifying vulnerabilities before they are exploited, organizations can take preventive actions, reducing the risk of data breaches and system compromises. - Regulatory Compliance
Many industries require regular security assessments to comply with regulations like HIPAA, PCI-DSS, and GDPR. Vulnerability analysis helps meet these compliance requirements. - Cost Savings
Addressing vulnerabilities early is far less expensive than dealing with the aftermath of a cyberattack, which may include legal fees, loss of reputation, and data recovery costs. - Continuous Improvement
Regular analysis enables organizations to adapt to new threats and improve their security policies and infrastructure over time.
Types of Vulnerabilities: –
Understanding the different types of vulnerabilities helps ethical hackers better adjust their analysis. Common categories include:
- Software Vulnerabilities: Bugs, buffer overflows, and code injection flaws in applications and operating systems.
- Configuration Errors: Default passwords, open ports, unnecessary services, and misconfigured access controls.
- Human-related Vulnerabilities: Social engineering risks, phishing susceptibility, or poor password hygiene.
- Network Vulnerabilities: Open ports, weak encryption, outdated network protocols.
- Physical Vulnerabilities: Unsecured access to servers or network hardware.
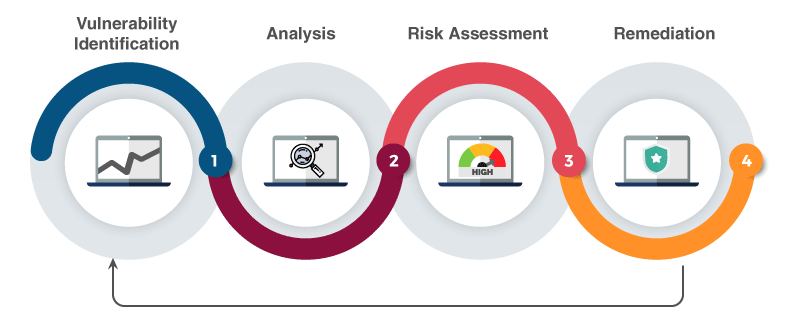
The Vulnerability Analysis Process:
The process of vulnerability analysis generally follows a structured approach:
- Information Gathering:
This phase involves collecting data about the target system, such as IP addresses, software versions, operating systems, and network architecture. Techniques include:
- Passive Reconnaissance (e.g., WHOIS lookups, DNS queries)
- Active Scanning (e.g., ping sweeps, port scanning)
- Scanning and Enumeration:
Using specialized tools, ethical hackers scan the system to detect vulnerabilities. This includes:
- Port scanning to discover open ports
- Service detection to identify software running on those ports
- OS fingerprinting
- Vulnerability Detection:
Tools and databases like CVE (Common Vulnerabilities and Exposures) are used to match system data with known vulnerabilities. This step identifies what flaws exist and where they are located.
- Analysis and Risk Assessment:
Each identified vulnerability is assessed based on its potential impact and likelihood of exploitation. This includes:
- Assigning severity ratings (e.g., using CVSS scores)
- Prioritizing vulnerabilities based on business impact
- Reporting and Documentation:
Findings are documented in a detailed report that includes:
- List of identified vulnerabilities
- Severity levels and potential impact
- Proof of concepts (PoCs)
- Remediation recommendations
- Remediation and Reassessment:
The organization applies patches, updates, or configuration changes to fix vulnerabilities. Ethical hackers may then re-assess the system to ensure the vulnerabilities have been effectively addressed.
Tools Used in Vulnerability Analysis:
Ethical hackers rely on a variety of tools to perform vulnerability analysis efficiently. Some widely used tools include:
- Nmap: A powerful network scanner used to detect live hosts, open ports, and services.
- Nessus: A popular vulnerability scanner that identifies security issues in systems and applications.
- OpenVAS: An open-source vulnerability scanner offering in-depth assessments and reports.
- Nikto: A web server scanner that checks for outdated software, misconfigurations, and dangerous files.
- Metasploit: While primarily used for exploitation, it also includes modules for identifying and verifying vulnerabilities.
- Burp Suite: Useful for analyzing web application vulnerabilities such as SQL injection and cross-site scripting (XSS).
- QualysGuard: A cloud-based platform offering automated scanning and vulnerability management.
Challenges in Vulnerability Analysis:
Despite its importance, vulnerability analysis presents several challenges:
- False Positives and Negatives:
Automated scanners may sometimes report vulnerabilities that do not exist (false positives) or miss actual threats (false negatives), requiring manual verification.
- Constantly Evolving Threat Landscape:
New vulnerabilities emerge frequently, and keeping up-to-date requires constant learning and monitoring of threat intelligence sources.
- Complex Environments:
Modern IT environments may include cloud infrastructure, IoT devices, and legacy systems all of which may have different vulnerabilities and require tailored analysis.
- Resource Constraints:
Conducting thorough vulnerability assessments requires skilled professionals and sufficient resources, which smaller organizations may lack.
- Integration with Business Processes:
Security measures must be aligned with business goals. Overzealous analysis or remediation may disrupt operations if not carefully managed.
Best Practices for Effective Vulnerability Analysis:
To maximize the effectiveness of vulnerability analysis in ethical hacking, consider the following best practices:
- Automate Where Possible
Use automated scanners to quickly identify common vulnerabilities, freeing up time for deeper manual analysis. - Update Tools and Databases
Ensure all tools are up-to-date with the latest vulnerability definitions and signatures. - Perform Regular Assessments
Vulnerability analysis should be a continuous process, not a one-time event. Schedule regular scans to keep systems secure. - Prioritize Based on Risk
Not all vulnerabilities are equally dangerous. Focus on fixing those with the highest impact first. - Combine Automated and Manual Testing
Human intuition and expertise are essential for spotting complex or context-specific vulnerabilities that tools may miss. - Document Everything
Maintain comprehensive records of findings, actions taken, and improvement recommendations. This helps in audits and future assessments. - Educate and Train Staff
Security awareness among employees reduces human-related vulnerabilities and fosters a security-conscious culture. - Use Threat Intelligence
Incorporate real-time threat intelligence to understand current attack vectors and focus your analysis accordingly.
The Role of Vulnerability Analysis in Penetration Testing:
Vulnerability analysis is often an initial step to penetration testing (pen testing), where ethical hackers attempt to exploit discovered vulnerabilities to demonstrate real-world risk. While vulnerability analysis identifies the “what,” pen testing addresses the “so what” by showing potential consequences of exploitation.
Both processes are critical components of a comprehensive security assessment strategy, with vulnerability analysis laying the groundwork for deeper testing and mitigation.
Final Words :
Vulnerability analysis is a cornerstone of ethical hacking and an essential part of modern cybersecurity practices. By systematically identifying and addressing system weaknesses, ethical hackers help organizations stay ahead of threats, protect sensitive data, and maintain business continuity.
In Today, cyber threats are more advanced than ever, so checking for weaknesses in systems regularly and carefully is not just a good idea it’s essential. By using the right tools, having skilled people, and following smart strategies, organizations can find and fix problems early. This helps them stay strong and secure in the digital worl.